
Today, Australia woke up to the news of a major cyber-attack against the country. The government has urged organisations to take precautions as they might need to take extra steps to protect their technology networks.
Although it’s still early days and not many details have been revealed by the Australian Government, this threat is understood and classified as a “sophisticated state-based cyber-attack” due to “the scale and nature of the targeting and the tradecraft used”, said the Prime Minister, Scott Morrison
Furthermore, according to Mr. Morrison this type of activity is not new, however, “the frequency has been increasing.”. Which further highlights the need for organisations to better manage risks by protecting their assets and data, while improving their security posture.
WHAT IS A STATE BASE ACTOR?
A state-base cyber actor refers to someone acting on behalf and supported by a government or a government body they represent. They can be “overt or covert intelligence, military or diplomatic functionaries.” (1)(2)
HOW CAN AUSTRALIAN ORGANISATIONS PROTECT THEMSELVES?
Not much has been revealed on who is responsible for the attacks, however, Australia’s Minister of Defence, Linda Reynolds has urged Australian organisations to protect themselves and take the necessary steps to protect their networks.
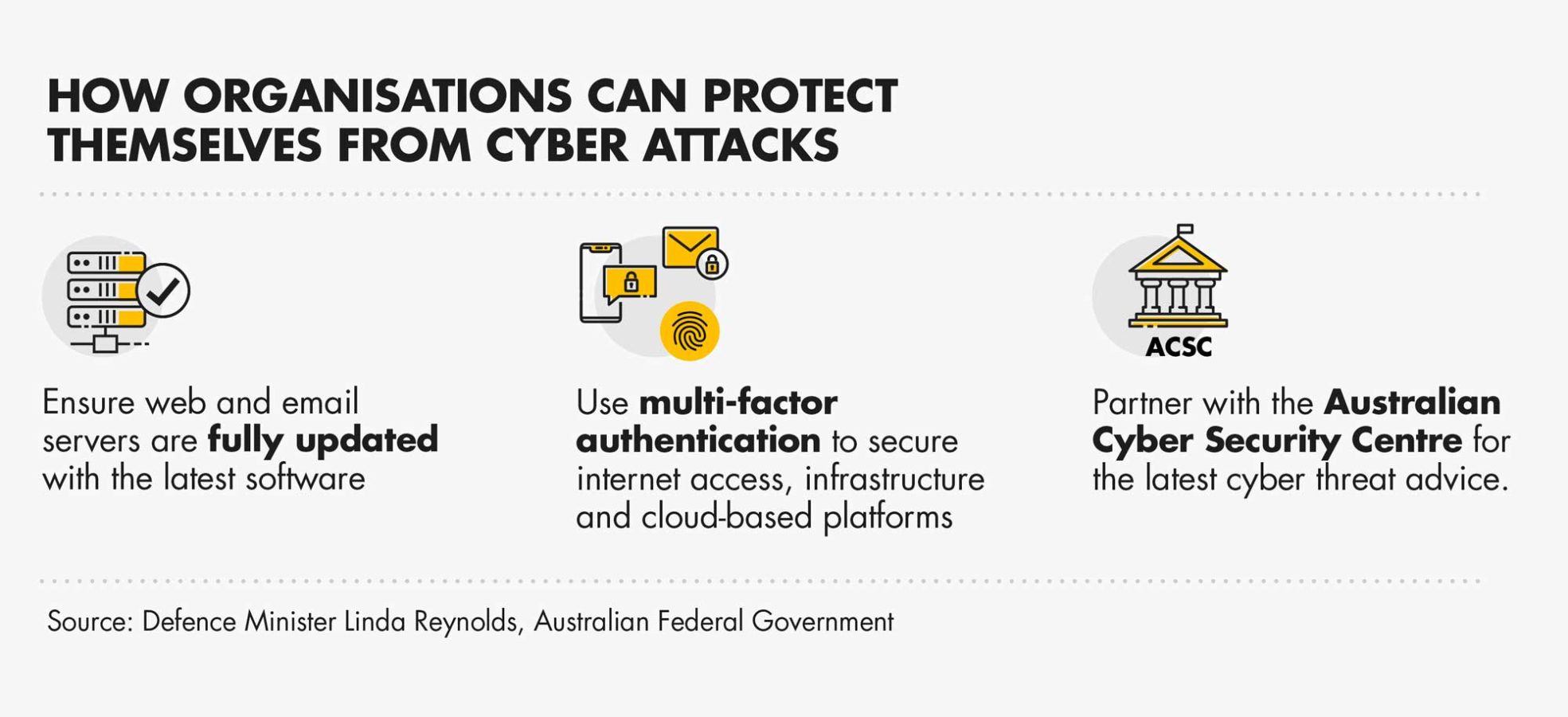
According to Ms. Reynolds, it is important that organisations take the following 3 steps:
- Ensure that any web or email server are fully updated with the latest software.
- Ensure the use of multi-factor authentication to secure your internet access infrastructure and cloud-based platforms.
- Become an Australia Cyber Security Centre (ACSC) partner to ensure they can get the latest cyber threat advice, to protect their organisations online.
THINK YOU MIGHT BE AT RISK? TALK TO US TODAY!
At Nexon, we take pro-active steps to ensure a robust cyber-security posture to all of our customers and we offer a comprehensive range of services to detect and prevent threats, reduce vulnerabilities and maintain visibility and control of their operational environment and data.
Visit our Cyber-security services page here
(1). 9News: Cyber attack Australia: What is a state-based actor and who could be responsible?
(2). 9News: Cyber attack Australia: Three steps Australians need to take to protect themselves
More articles to explore


