We always look forward to the Annual Cyber Report from the ACSC, as it shares important insights into the changing threat landscape and type of attacks. Of course, we see this evolution every day in our SOC, and over the last year, we’ve observed our own changes in the type and scale of attacks happening in Australia and beyond.
So, what has changed this year?
There are some subtle changes in this year’s report, driven by the shift in the geopolitical landscape, escalating different kinds of attacks and risks to every day organisations.
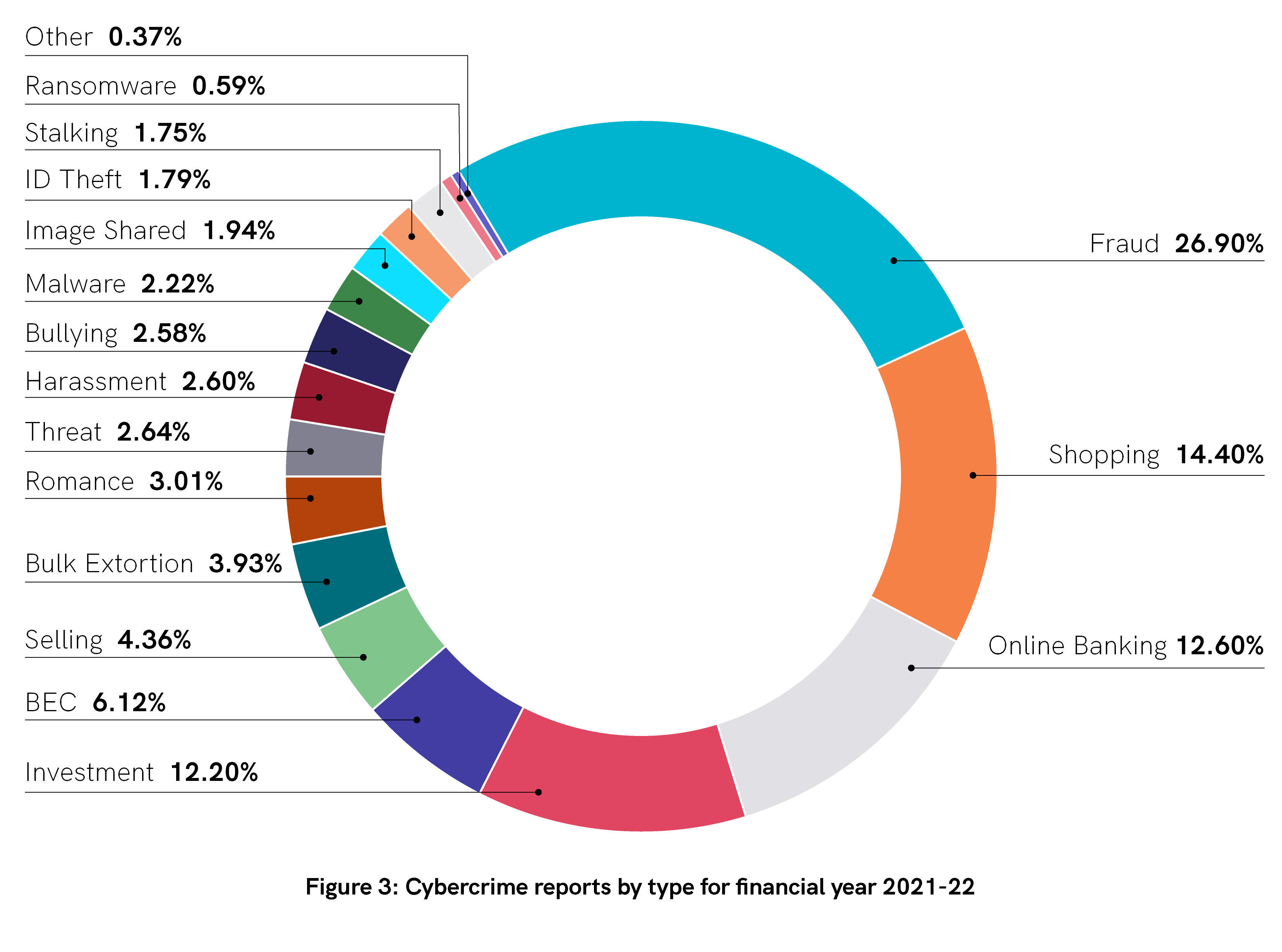
This chart from the ACSC shows a breakdown of the types of cybercrime reports registered in the last 12 months.
The highest three ranking segments are Fraud, Shopping and Online Banking. Yet the focus of the report continues to be on Ransomware. Let’s understand why.
Ransomware Rules
According to these statistics, Ransomware reports make up 0.59% of all cybercrime reports. Regardless of the low volumes, it’s the most destructive of all attacks. We only need to look at recent cases in Australia to substantiate this premise and understand the far reaching impact of such an attack. From Brand and reputational damage through to customer loyalty, financial losses, and downtime, the impact cannot be ignored.
Front Line Vulnerability Matters
There has been a marked increase in Business Email Compromise with financial losses escalating to over $98 Million with the highest number of reports coming from Queensland. The compromise of a single person in an organisation or, group of organisations with a global parent are real and happening every day. In a business without protection, this could be the end of trading.
Cybercrime as a Service (CaaS)
CaaS is on the rise. These packaged attack focused outsourced or hybrid services can provide low skilled attackers with enough tools and information to facilitate cybercrime with very low barriers to entry. It also allows people with high quality skills to monetise their expertise in hacking or other illegal cyber activities, while enabling cyber criminals to outsource elements of operations in which they are unskilled from the black market.
Targeting Essential Services
As with last year’s report, cyber security incidents by sector are Commonwealth and State / Local Government, with Health Care and Social Assistance, Information, Media and Telecommunications and Electricity, Gas, Water and Waste making it into the Top 10. The continued focus on compromising critical services is a continuing risk which must be addressed by these Sectors.
Our Advice?
-
Active and Escalate Security Controls and Systems
We recommend moving away from reliance on passwords to Multi Factor Authentication (MFA). Also apply the principle of least privilege to people and processes in your organisation. Don’t give administrators access to email or online services if they don’t need it.
-
Ransomware is here to stay – create a response plan as priority
If you look at the actual likelihood of any organisation receiving a ransomware attack it’s pretty low. But the impact is extreme. In simple terms, one attack could take you under. What matters is making a plan for if and when you are attacked. How and to whom do you disclose? Who’s communicating internally and externally? How do we assess damages based on data stolen? Have we got detection in place? What does our insurance cover? If you don’t have a response plan, create one today.
-
Patching is everything – increase your speed to deploy in <48 Hours
Patching really is a fundamental that cannot be ignored. The inherent risk of waiting for 6 – 12 months to shorten the patching process is too much. Where possible, organisations of all sizes should be patching within 48 hours where an exploit exists. And prioritising security patches for remote access products is critical. If you don’t have a response plan, create one. The focus of organisations should be on preventing and also preparing
-
Make Cybersecurity a strategic priority – deploy the right technologies, team and controls
Organisations need to harden their systems by eliminating attack vectors and reducing the potential attack landscape. The evolution in attack sophistication and speed means organisations can no longer be complacent.
-
Be prepared for every eventuality – ask for help to ensure you’re protected.
Improving performance, productivity and protection should be a business imperative. Without a strong advisory team, watertight cybersecurity strategy and skilled operational team / SOC monitoring your 24 x 7, you’re running a risk you can’t afford to take.
Would you like to know more? Talk to us for more support or guidance.
More articles to explore